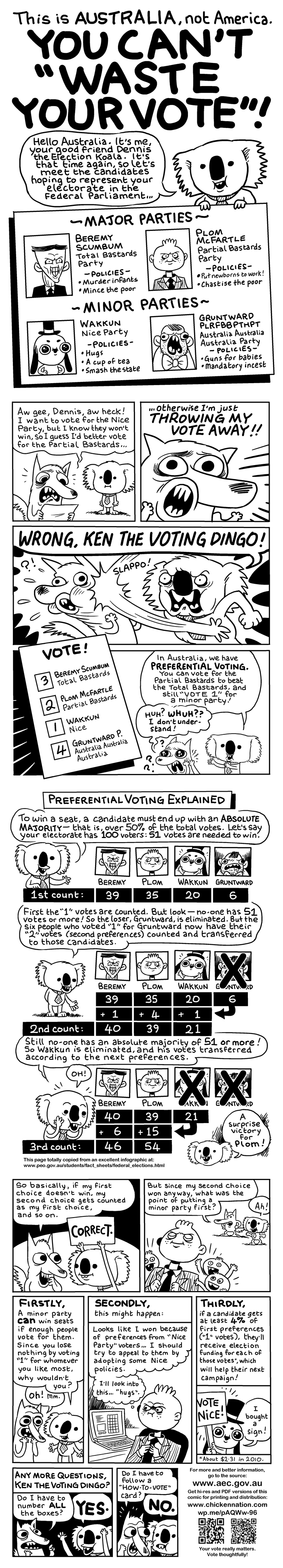
There are two ways to vote for the Senate in Australian elections. One way (“above-the-line”) is simple and quick, but it means the politicians you vote for get to control who gets to use your vote if they don’t win. Why should you hand your power over to them like that? The other way gives you 100% control: it’s called “below the line” voting, but it’s a lot more involved. Here in the state of Queensland, we have 82 people running for the Senate in this Saturday’s election, so if I want to vote “below the line”, I have to fill out every single box next to each candidate’s name, from 1 to 82.
This is complex, so only about 3.8% of people do it across Australia. And it still has disadvantages. Even if I have no strong opinions on more than a few parties, or even if I ONLY want people from a few parties to get in and actively don’t want anyone else to use my vote, I still have to pretend that I like the person who gets my “50” vote more than the one who gets my “82” vote. I’m pretty interested in and engaged with politics, but there’s no way I have an opinion on 82 different people. There’s only ten people I actively want to support in this election, and I reckon groups like Family First and One Nation are just as bad as each other. So are parties like the Sex Party, Animal Justice Party and Senator Online Party, who did grubby deals that give One Nation’s Pauline Hanson a very good chance of winning a seat.
Fortunately, there’s a little trick hidden away in the law about how the votes are counted. The trick is probably meant to make sure people who make honest mistakes filling out the ballot paper still get to have their vote counted. But we can manipulate this trick to make sure that only the people we actually WANT to vote for get to use our vote.
THE TRICK:
1) Vote for the candidates you actually want to get in. I have ten people I want to support, so I am going to vote 1-10 for them.
2) MAKE A DELIBERATE MISTAKE. The best way (in my case) is to write down the number 11 twice.
3) Then you have to fill in all the rest of the boxes. The order does not matter one bit, so you can just start from the left and go to the right. But you HAVE to fill them all in consecutively. I’m going to start from 13, so that I know the last number I write still has to be 82. You can also write from 12-81, as Dr Cam Sexenheimer pointed out on Twitter this morning.
So, what exactly will this do, and what are the risks?
It means that only the top ten people I voted for will get to use my vote. If none of them get elected, my vote will just drop out and not go to anyone. Because I voted “11” twice, the rules say the vote-counters can’t know who I wanted to “really” vote for. But the other rule they put in to make sure votes with a couple of honest mistakes get counted means my vote gets counted, too.
Yes, but what about the risks?
The first risk is that you make too *many* errors and your vote doesn’t get counted at all. The rule says that IF:
You could correct three (or fewer) of the numbers on your voting paper,
and IF those corrections would mean 90% or more of the numbers were filled out properly
THEN your vote counts.
That means if you made FOURTEEN numbering errors (including your deliberate error), your vote would simply not be counted at all. For instance, if you voted 1,2,3,3,3,3,3,8,9,10… your vote WOULD be counted because changing three of your numbers would mean 90% or more of the boxes were filled out correctly. But if you voted 1,2,3,3,3,3,3,3,3,3,3,3,3,3,3,3,17,18,19… your vote would NOT be counted because changing three numbers would still leave ten boxes labelled incorrectly, and 10 out of 82 means you’ve only filled in 88% of the boxes correctly.
Yes, that’s a little complex. So if you’re going to take advantage of this hack, make sure you only make ONE error, the deliberate error. Because if you vote this way, and if the race is tight when your vote gets counted, there will be angry, smart politicians who know the rules backwards arguing VERY LOUDLY INDEED about whether your vote is valid or not. So why give those major-party-mongrels the pleasure of throwing your vote out?
There’s also a deeper risk I should mention. When you run for the Senate, you normally have to get about 14% of the vote to win. If none of the people you vote for wins a seat, your vote drops out of the count completely. That means the 14% someone needs to win gets a tiny bit smaller. If, say, 100,000 people were to vote this way in Queensland, and all their votes dropped out, that means the candidates still in the race would need about 14,000 fewer votes to win a seat. It’s practically impossible to predict beforehand how this sort of thing is going to play out at an election, with complex interlocking preference deals between dozens of different parties, but it could possibly lead to weird results you don’t want.
So, think about those risks before you do this. I’m prepared to risk it myself, so I am definitely going to vote this way. It’s not a huge thing really, but it’s good to be able to assert control over my life in small ways, and large ones too.
NOTE: Amusingly enough, I got turned onto this trick by the loathsome @Karwalksi of the Wikileaks Party, who thinks exposing their website’s visitors to US Government spying is cool and edgy.
NOTE: Similar info to this was published over a week ago on the Indpendent Australia website. However there are errors in that post, including the idea that the revolutionary communist activist formerly known as Albert Langer (who now chooses to be known as Arthur Dent, NOT “Albert Langer”) “discovered” this loophole.
SOURCES:
1) Tweets from the Australian Electoral Commission this morning:
2) The official guidelines the Electoral Commission use to decide if a vote gets counted or not